Every time you go online, you leave behind digital traces—like footprints in sand. These invisible markers tell a story about […]
Why Your Home Router Needs More Attention Than You Think
Your home router is like the front door to your digital life, yet most people set it up once and […]
The Hidden Dangers of Public Wi-Fi in 2025: Are VPNs Still Enough?
Public Wi-Fi networks have become a necessity in coffee shops, airports, hotels, and even city-wide hotspots. However, as cyber threats […]
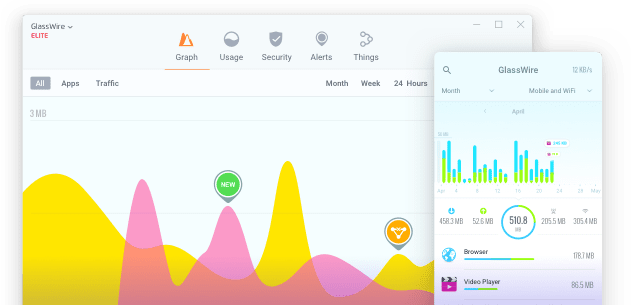
Hidden Bandwidth Hogs: Apps & Devices That Secretly Drain Your Internet
Slow internet speeds can be frustrating, especially when you’re not sure what’s causing the problem. While streaming services and downloads […]
Improving Network Privacy in Shared Spaces
In a world increasingly dependent on internet connectivity, network privacy has become a critical issue, especially in shared spaces where […]
Cybersecurity in the Cloud Office: Safeguarding Data Beyond Company Walls
Today, more and more businesses choose to run their everyday operations in the cloud. The cloud is easy to scale, […]
ARM Device Support, Snooze GW Alerts, Protect Tab Upgrades, and More
At GlassWire, we’re constantly striving to improve your experience with powerful features and intuitive design. Our latest update introduces ARM […]
Holiday cybersecurity: Protect Yourself from Phishing Scams While Shopping Online
The holiday season is here, bringing joy, festive lights, and unfortunately, an increase in online scams. Cybercriminals thrive during this […]
How IP Addresses Help Detect and Prevent Cybersecurity Breaches
Users may feel well hidden when they are browsing online, but their digital activity is not anonymous at all. Actually, […]
GlassWire Enhanced Network Scanner
With the latest update, we are glad to introduce a suite of new features designed to enhance device discovery and […]
Cybersecurity Basics: Safeguarding Your Personal Information
Every 39 seconds, a cyberattack happens. Now, think about your passwords, bank details, and personal data. How secure do you […]
The Rise of Zero Trust Architecture
Traditional cybersecurity models are starting to show their age. The days when a sturdy firewall and a strong perimeter were […]